In this post, I’m going to write about Sensitivity Labels, which have seen the most change this past year. Sensitivity Labels are powered by Microsoft Information Protection (MIP, formerly Azure Information Protection, AIP) and were previously only available with additional Azure licensing, or a bundling of 365 + Azure. Now, with the advent of Unified Labeling, Sensitivity Labels are available for configuration and use in Office 365 natively, as well as in MIP.
Unified Labeling
Unified Labeling earns its name by putting the same labels in both Office 365 and in Azure (MIP). It can be a little confusing because it’s not “unified” in the sense of having one set of labels for both sensitivity and retention; it’s unified in the sense that the sensitivity labels and label policies in 365 are the same as what’s in Azure. While there’s some nuance in how they get published to their respective workspaces and endpoints, they are the same labels.
Labels and Label Policies
Just like Retention Labels, Sensitivity Labels consist of both the labels themselves and the policies the publish them.
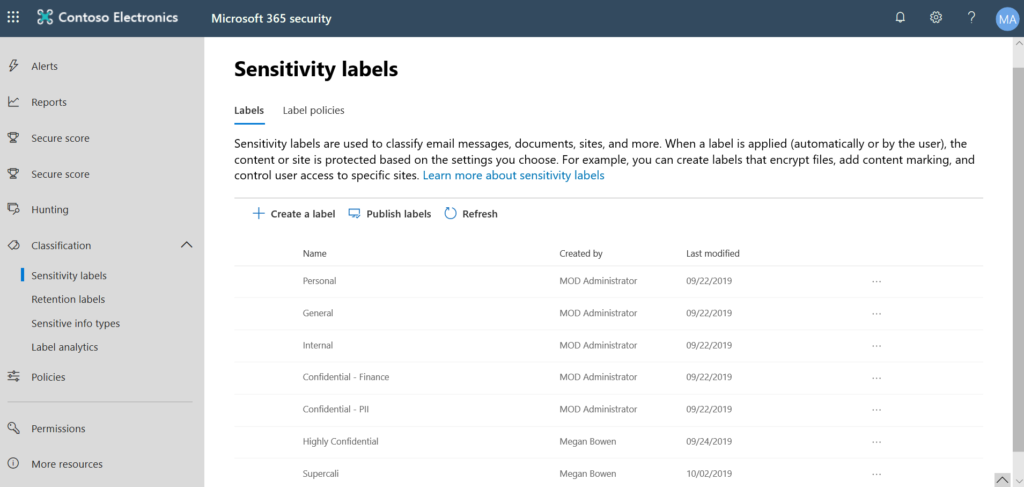
Each label has a display name, optional tooltip to tell end users what it’s for, and some additional capabilities such as encryption, watermarking, and data loss protection; optionally they can be applied automatically based on some rules, but I’ll save that for another time.
When one or more labels are published, they go into a label policy, which groups the labels, sets the scope of services and users they apply to, and define whether or not users must apply a label, and whether ot not they can lower the sensitivity classification.
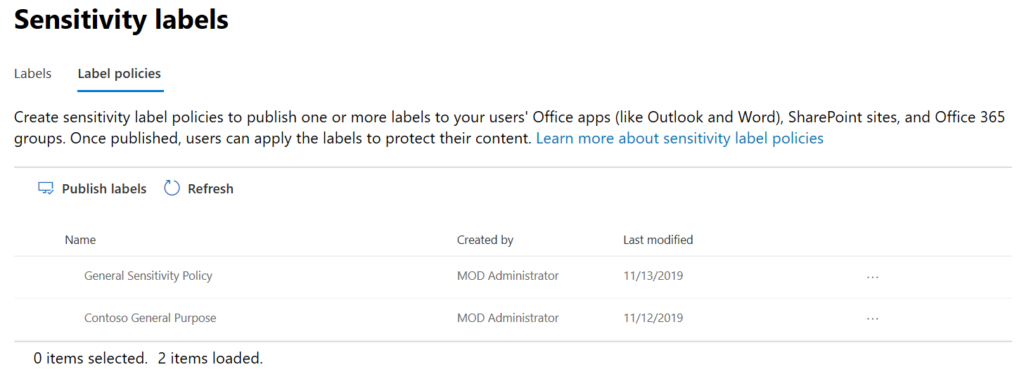
I wrote about labels vs policies very recently. Defining a sensitivity label policy for everyone, and then custom label policies for specific business units, is not uncommon.
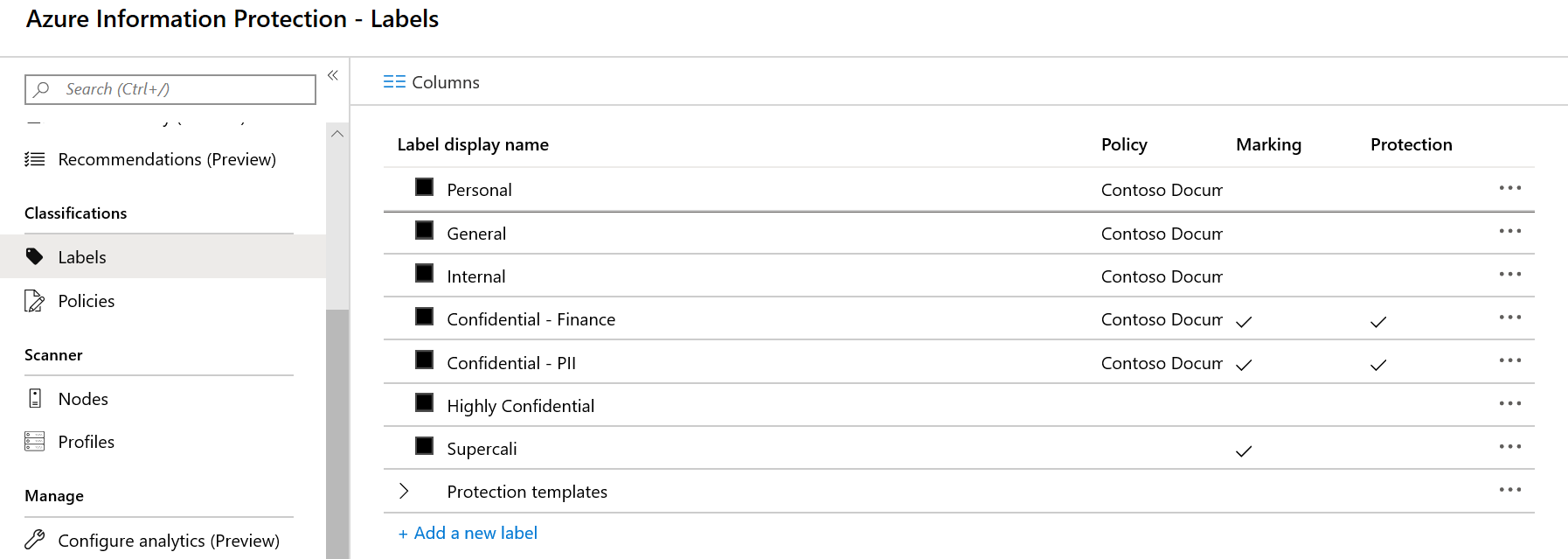
Now let’s take a look at these same labels and label policies in Azure Information Protection. To be real clear, I’m looking at the same labels and label policies in the upcoming picture as I did in the previous pictures.
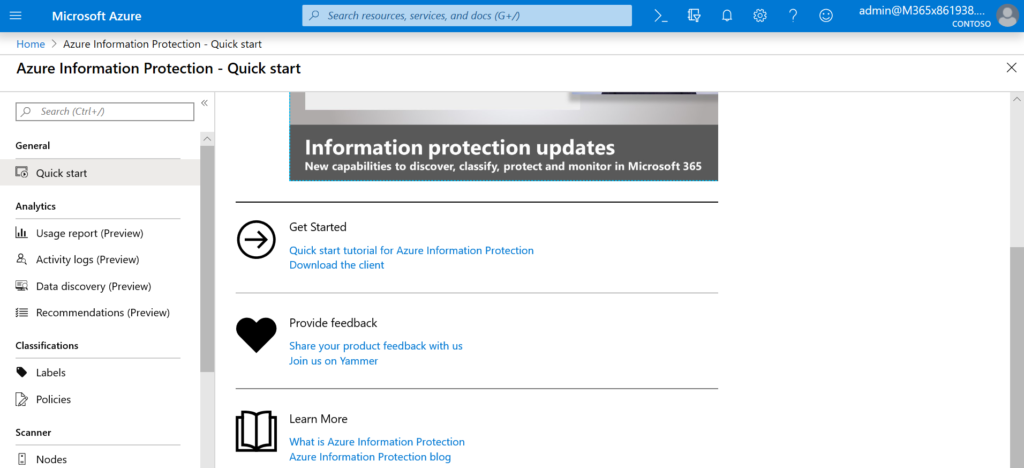
I can hear you scream and see you rolling your eyes. “I’m an Office 365 administrator, not an Azure Administrator!” Most organizations have dedicated teams for these platforms, and dediated teams for the various solutions in them. Relax, though: What we’re about to look at in Azure as 365 admins is actually very simple, and we probably won’t break anything.
I’m still logged in with my global admin account (top right) – the same account I logged into 365 with. My area of focus here in AIP (MIP) is classifications: labels and policies.
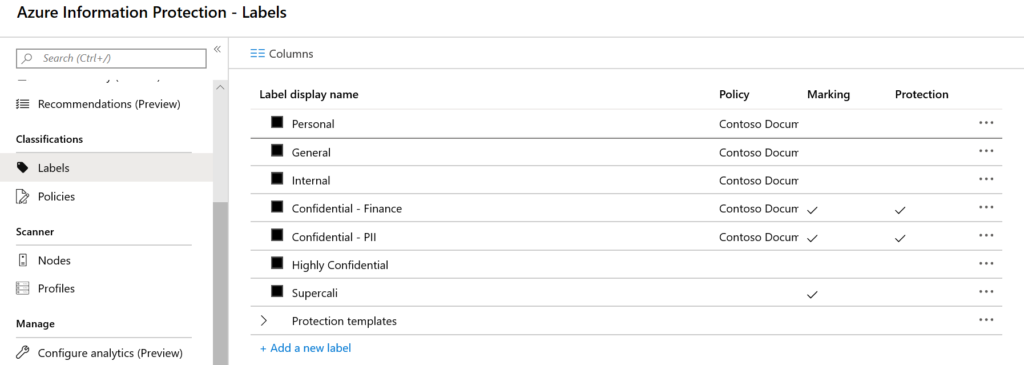
Here are all of my Sensitivity Labels. Remember my Sensitivity Labels in Office 365? They’re all here. They’re the same, and I can manage the labels here or in Office 365.
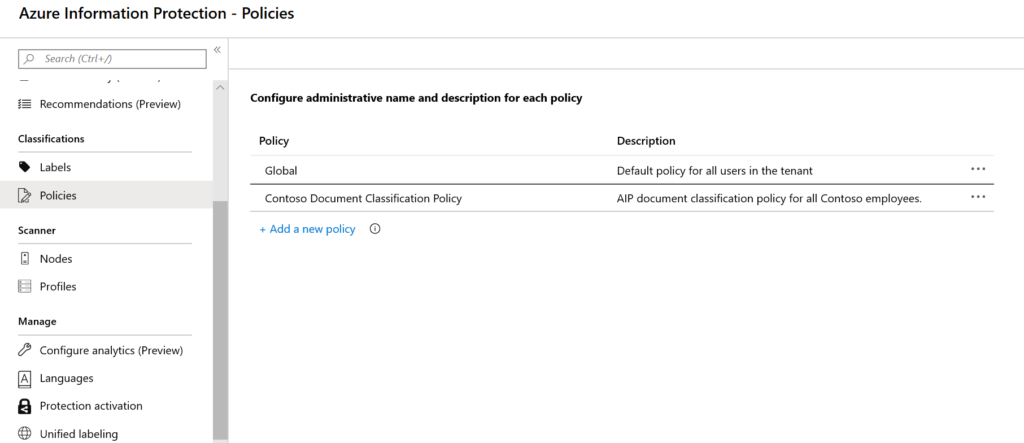
I’ve also got my Sensitivity Label Policies. Again, I can manage these in Azure or in Office 365.
This is what Microsoft means when they say “Unified Labeling”. Previously, there was no way to manage Sensitivity Labels in Office 365: they only lived in Azure, and while they could be used by Office 365, there was no way to configure them or the policies that went along with them.
These labels can be used for non-365 sources as well – yet another topic for another day – and there is some nuance over how these get published to workstations as opposed to Office 365 workspaces.
For most organizations, there will probably be some thumb-wrestling over who gets to make changes, or create new labels and label policies. Previously, there was probably an Azure team dedicated to these labels, and the 365 team (or SharePoint team, or Exchange team, etc) had to go to them.
It’s possible to security-trim this so that work is only done by an administrator in the respective space, or even force the old division of labor to persist.