While corresponding with an engineer looking to solve a particular use case, I decided to take a deep dive into Office 365’s Supervision function, to see if that would help.
The basic use case was: we want to redact, or at least take action of some kind, in the event that someone outside the organization emails sensitive information. An easy example would be, “if my customers email their credit card numbers to my employees”, redact, or at least take some kind of action.
So, Supervision: what is it?
Supervision
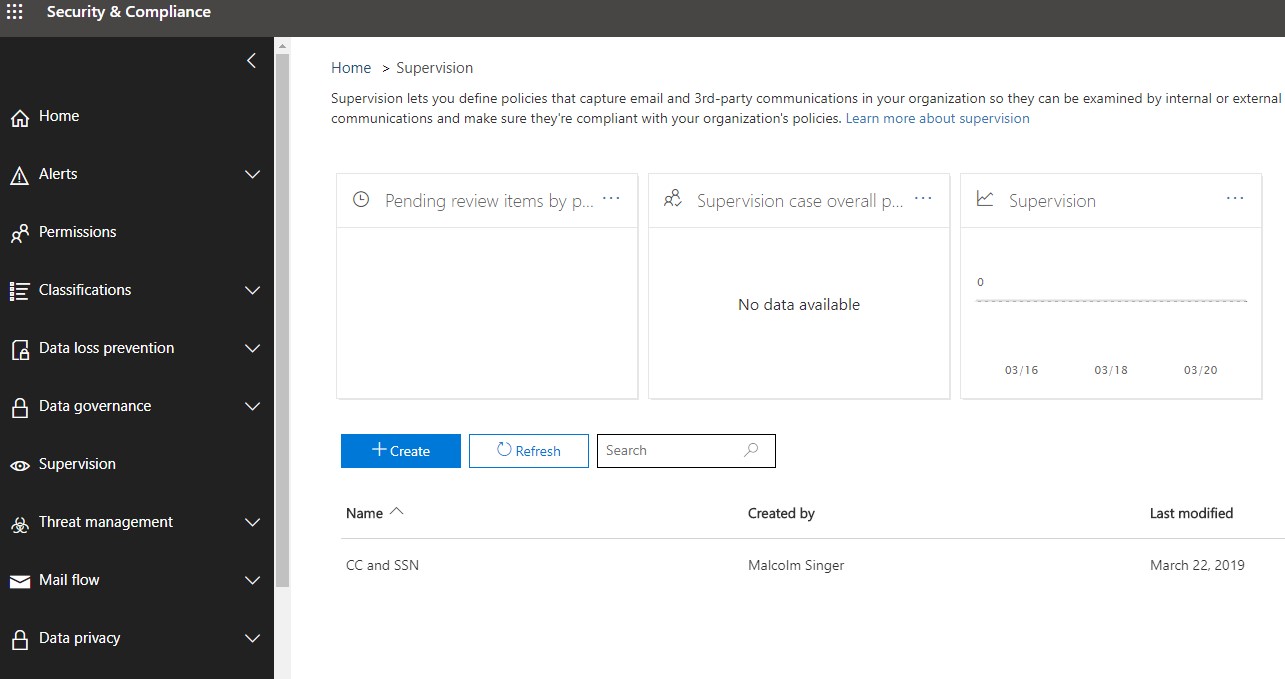
Supervision has been part of Office 365 since 2017, but it recently underwent some improvements. The complete litany of functionality is laid out nicely in this Microsoft kb article.
In a nutshell, Supervision allows you to create Supervision Policies with a defined scope of users and their communications. Presently (March 2019) communications include email and Teams channels, inbound/outgoing/internal.
Microsoft says they also support third-party communications, but take a look at their diagram and decide for yourself how practical Supervision is for third party platforms, as opposed to best-in-class platforms for monitoring non-365 communications.
Supervision allows a defined group of supervisors to review communications and tag them as compliant, non-compliant, or questionable, and once a review of the monitored communications has been completed, mark the review as complete.
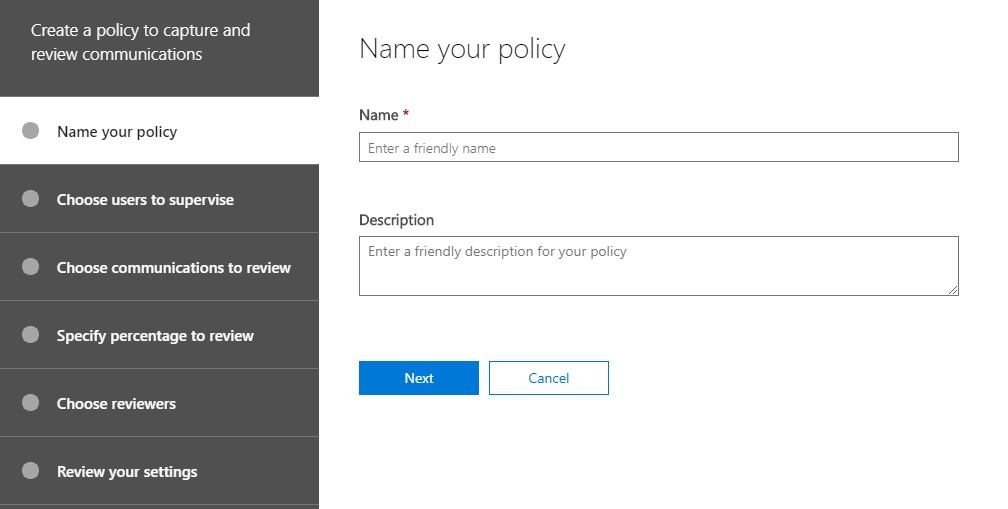
What does it look like? Let’s walk down the path of creating a policy.
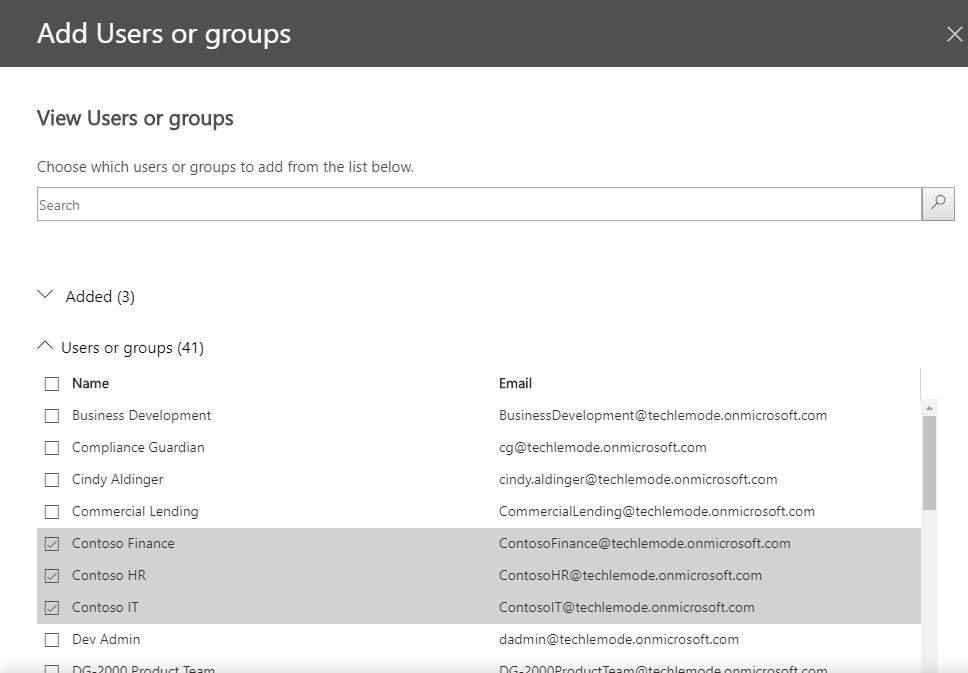
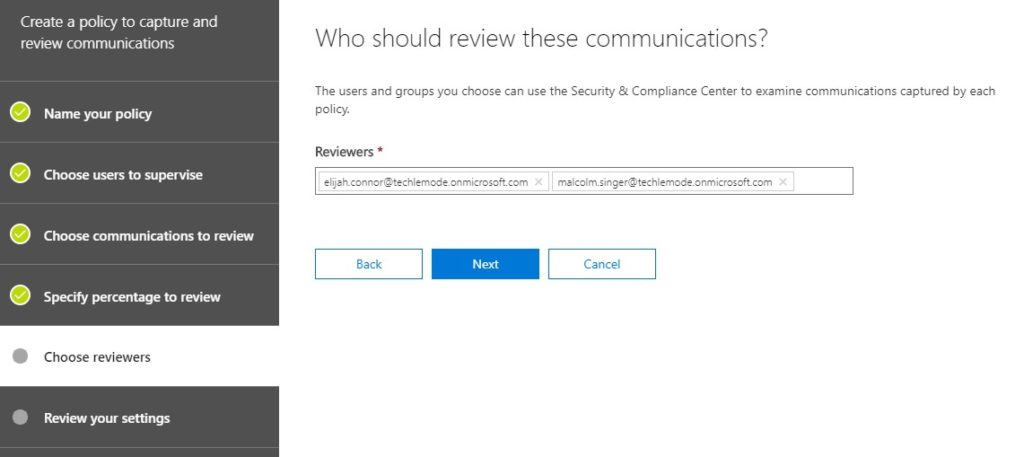
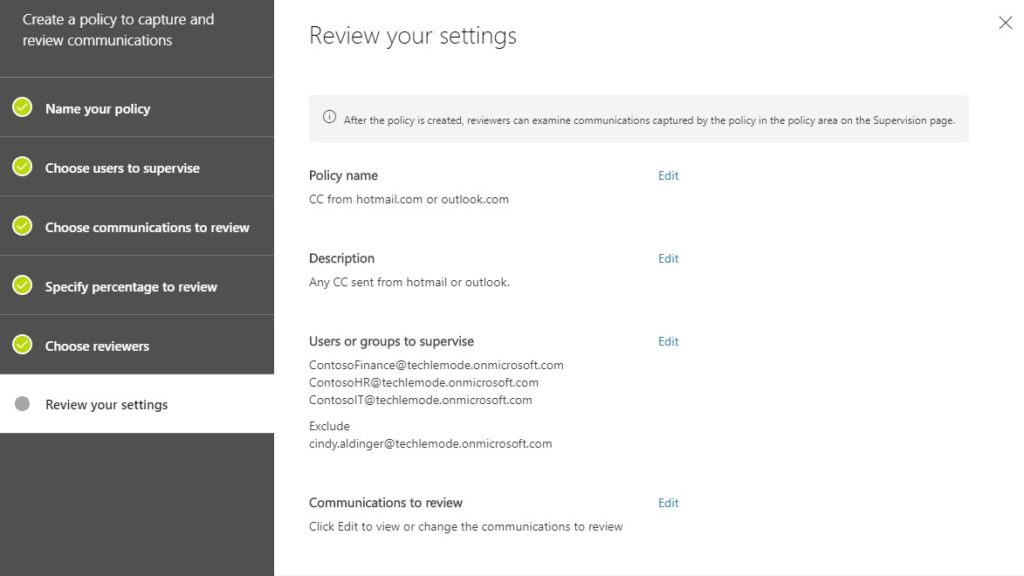
When adding Groups to supervise, you can also carve out users. In the image above, I selected the Contoso Finance, HR, and IT Groups. In the next image, I carved out Cindy Aldinger – she is exempt, regardless of which Groups in scope she might be a member of.
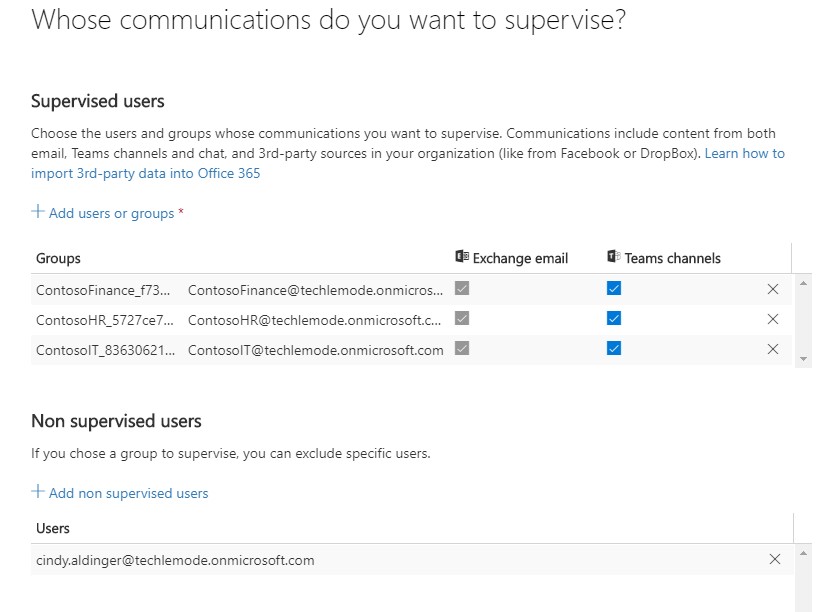
When selecting what you want to review, it’s important to note that you can specify any combination of inbound, outbound, or internal communications.These cover a range of use cases and, in practice, you’ll probably end up with multiple supervisory policies for any given scope. For example, you might be concerned with one class of data being inappropriately sent from the organization, and another class of data being shared internally among employees.
Because I work primarily with enterprise financial service customers, I’ll highlight a common use case: broker-dealer communications. Employees who are broker-dealers in a bank fall under additional SEC regulations that do not apply to other employees.
Another example would be “Chinese Wall” separations – a large finserv with multiple lines of business may want to ensure that investment bankers are not sending market-moving information over to the wealth management business.
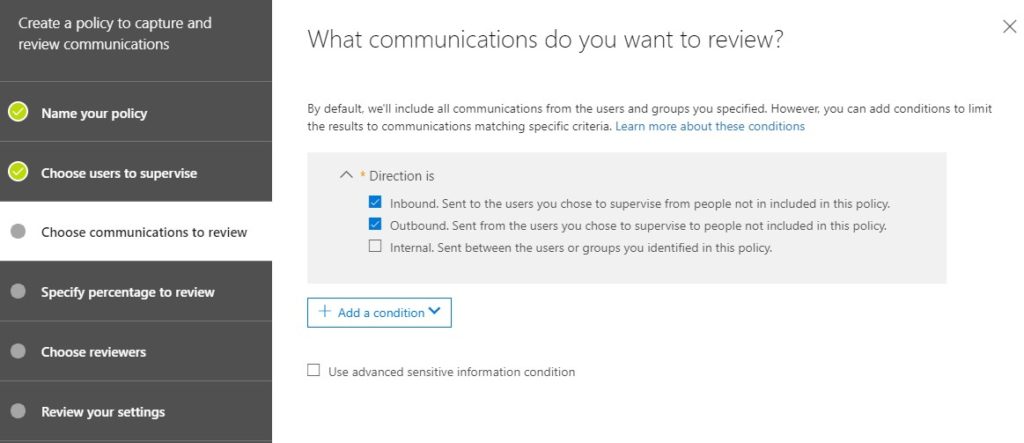
Also on this page is where you define what you’re looking for – several examples are in the dropdown list below. You can add multiple conditions. These rules stack – they’re all Boolean “OR”. For example, a policy could be “any email sent to domain contoso.com OR from northwindtraders.com OR larger than 128KB”. Perhaps in the future Microsoft will add some configurable Boolean logic, although that would make rule-making more complex and, arguably, to not much advantage.
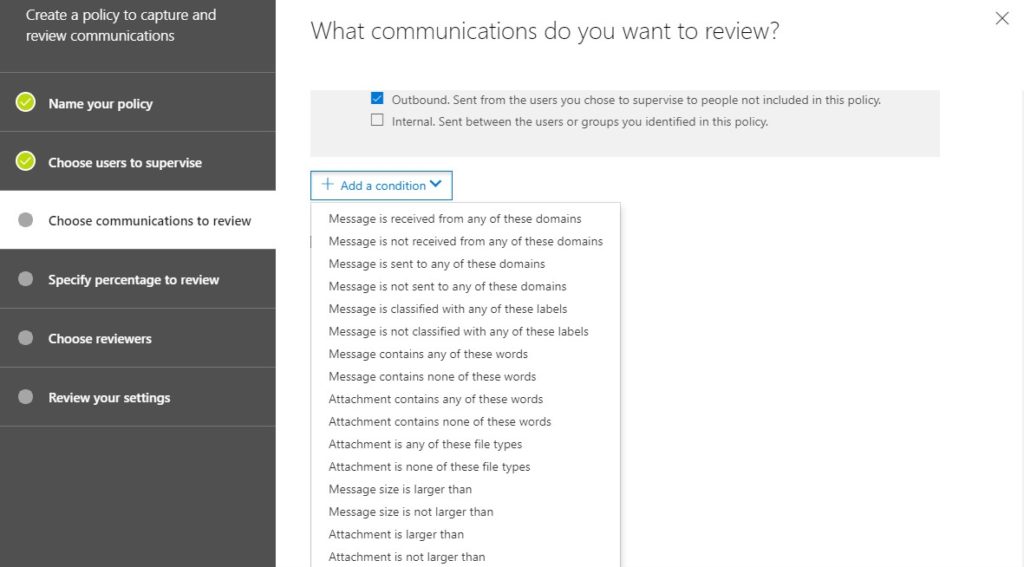
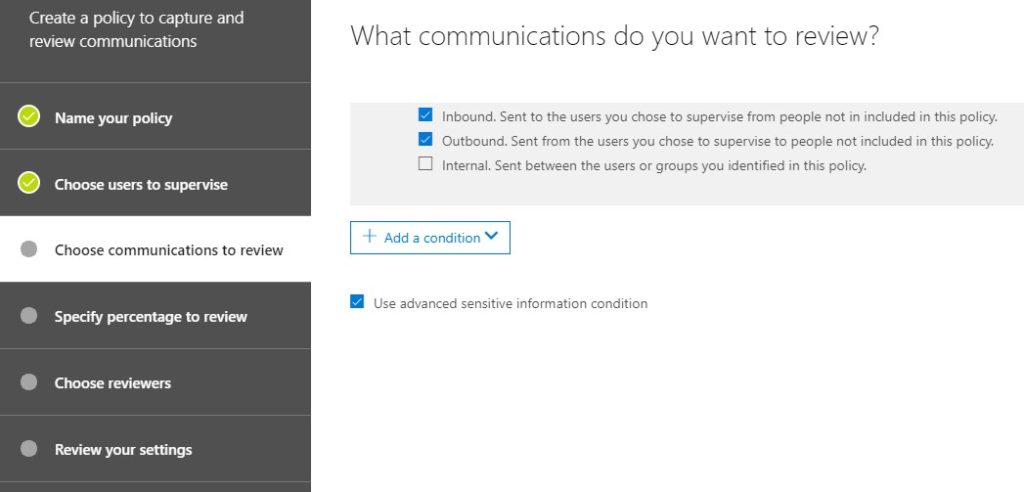
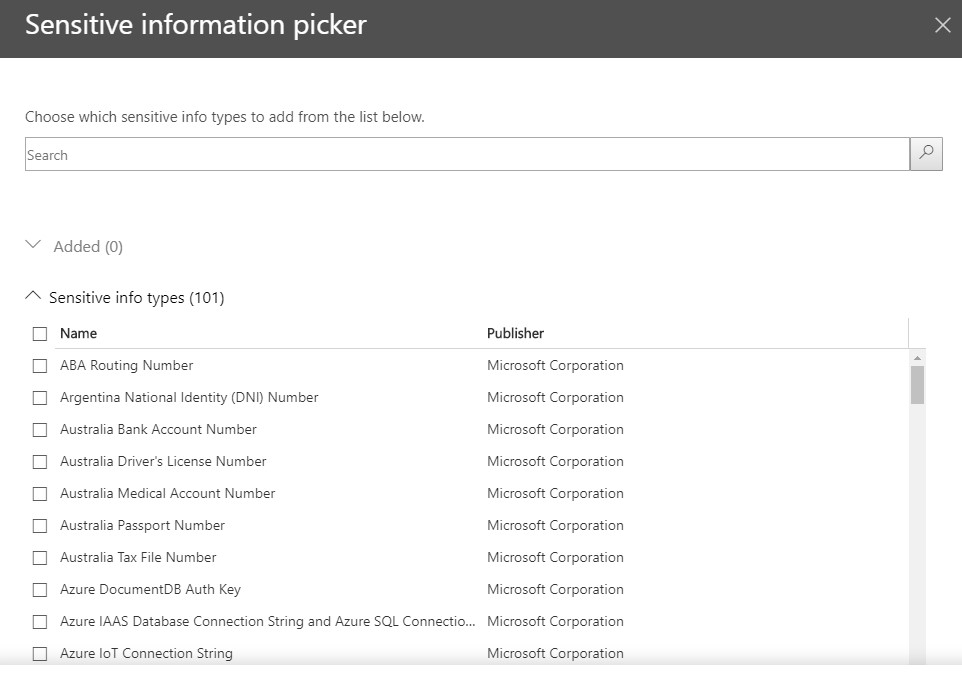
The criteria in the “add a condition” dropdown are pretty standard Exchange-type criteria, controlling communications based on information about the email and any attachments, or about the sender and receiver. If you want to use more sophisticated criteria from your Data Loss Prevention settings, check the “use advanced sensitive information condition”. Look familiar?
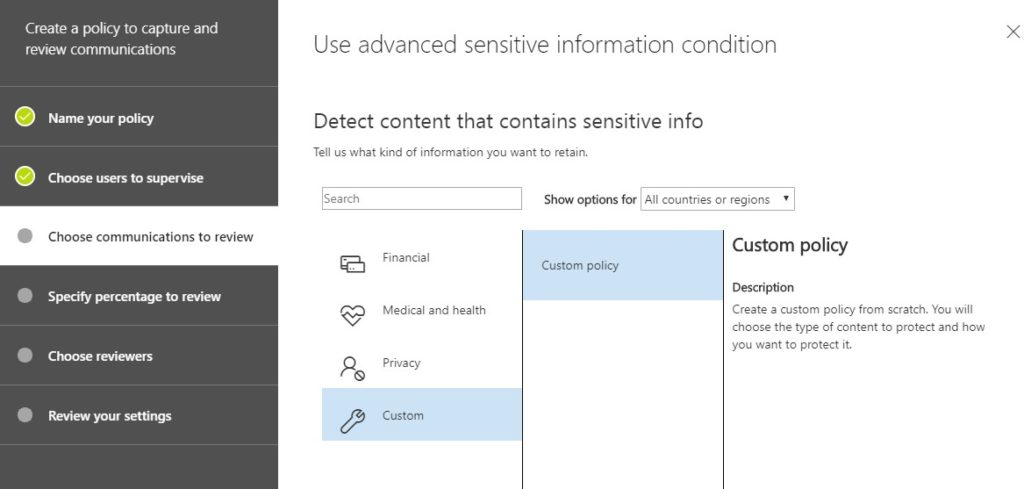
Microsoft provides a bunch of standard criteria under various categories. For example, under financial there are checks for Bank Routing Numbers, Credit Card Numbers, and so on. You can also create custom ones based on dictionary lookups or regular expressions. The good news is, if you were creating or using any of these criteria for using in your sensitivity labels, you can use them here as well.
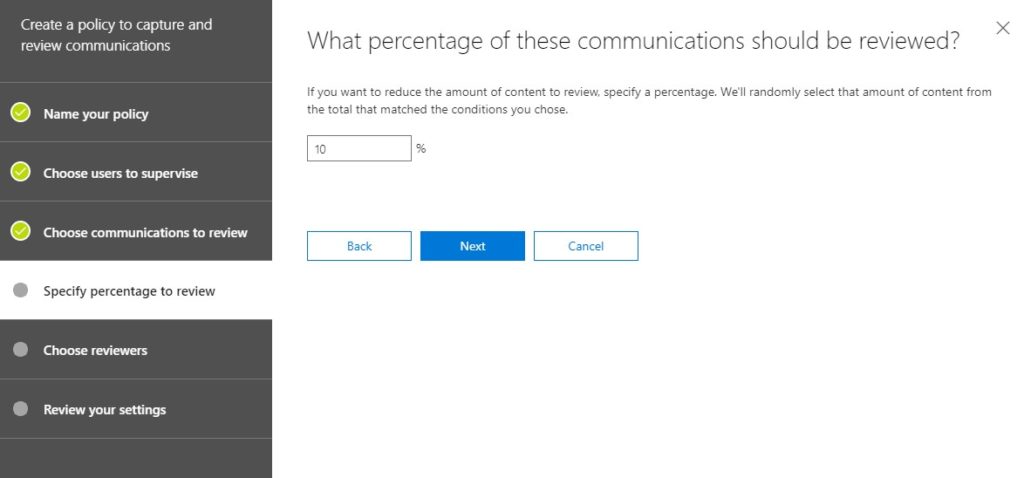
I thought this setting above was interesting. Typically my use cases are all-or-nothing: I want to see everything that matches XYZ criteria. However, in an environment where, for example, a manager is meant to keep tabs on employees, but trust them to do the right thing, setting a 1-in-10 or 1-in-5 ratio might make sense. Unless Supervision is a dedicated role, it might be more practical to only spot-check a percentage of communications.
At the end, you get a chance to review all your settings, then go back and edit anything you don’t like, or missed.
Voila, le Supervision Policy. What can you do with it? Let’s hop back to the Supervision pane.
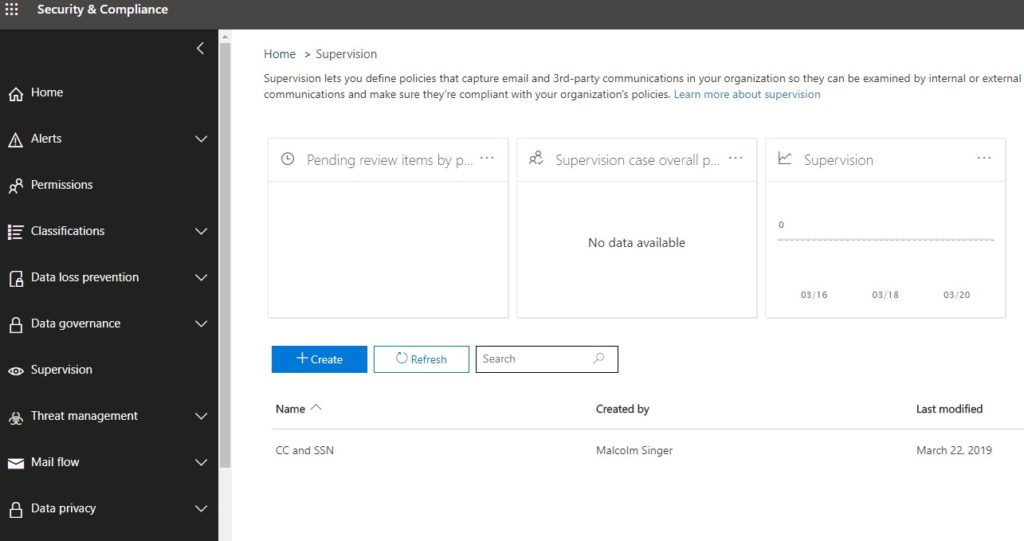
As items get flagged for supervision, they’ll show up in the “Pending” box. As cases are opened they’ll show up in the “Supervision” box. Lastly, the third box in the picture above will show a graph of cases over time. Theoretically, as you educate your users in proper etiquette, that line will trend down.
In the bottom rows are all the Supervision Policies that have been created. At this point in my screenshot safari, I’ve only created the one, CC and SSN. Remember my correspondent’s use case? Let’s see what it finds, by opening that Policy.
” . . . we want to redact, or at least take action of some kind, in the event that someone outside the organization emails sensitive information . . . “
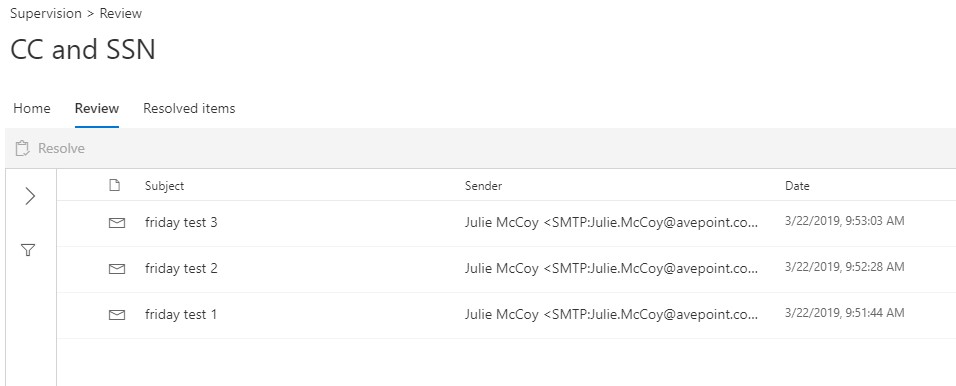
Joy! All of my test emails were caught. Since I’m(actually, my demo user, Malcolm Singer) flagged to review these, they show up under “Review”.
Note: there is a way to use a shared mailbox for items to be reviewed, and for reviewer to review them from Outlook or Outlook Web Access. I’m not going to get into that here.
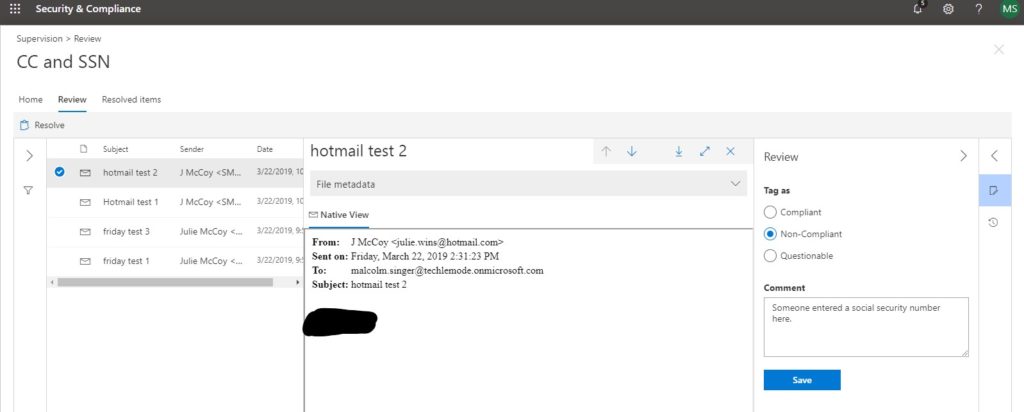
Here’s an example from an email I sent later. That big black smudge is some post-production redaction on my part, but everything else is part of Supervision.
Look at that – I can see the headers, the contents of the email, and I can tag this is the Review stage as Compliant, Non-Compliant, or Questionable. Note that tagging, in and of itself, does not resolve an item. That’s done by clicking on “Resolve”, on the left.
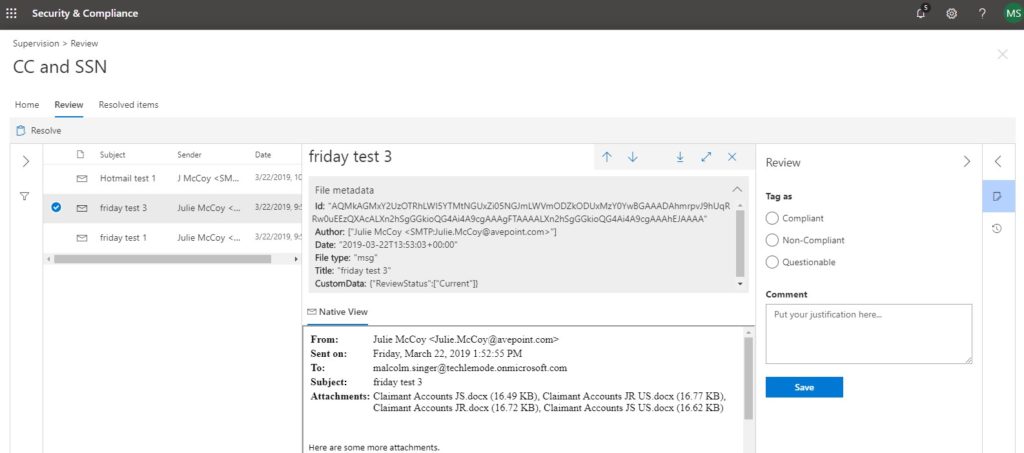
In another example email, I sent sensitive data in the attachments, but not in the body of the email itself. In this case, the message was caught, and I can still see metadata, but I don’t have visibility directly into the attachments. I have to trust that Supervision caught what it was meant to catch.
Was I able to automatically redact? No. Was I able to notify someone that a social security number or credit card number had been sent? Yes.
That’s Supervision in a nutshell. Clearly, there’s a lot of power to harness, but the controls an user experience are a bit lagging, even after a major overhaul in early 2019. The real challenge will be in either developing a business process (“how should we do supervision”) or adapting an existing supervisory process to Supervision (“we do it this way, but can’t do it exactly like that in Supervision”).