I recently had a call with a customer new to Office 365, and one of the services they wanted to make use of in Security & Compliance was eDiscovery. I realized that while I’ve used eDiscovery solutions from other vendors, I’d never actually built out an example in native Office 365. Off I went!
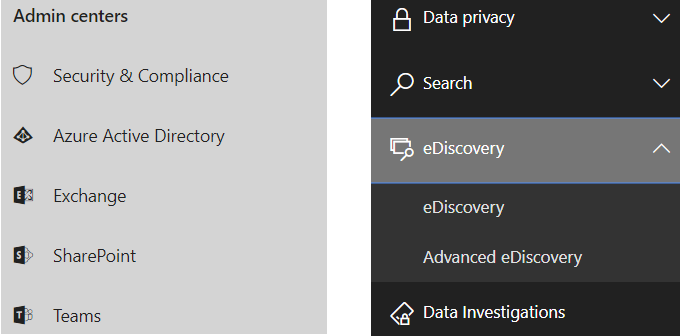
Office 365’s eDiscovery (and Advanced eDiscovery) services are located under the Security & Compliance admin center. Scroll down to “eDiscovery” and break it out to select the appropriate application – eDiscovery or Advanced eDiscovery. NOTE: Advanced eDiscovery requires either an E3 with Advanced Compliance add-on, or E5 license.
For those unfamiliar with ediscovery (as a process, not a specific solution), it’s basically a way to 1) prevent content relevant to an investigation from being disposed of, and 2) a way to allow users who are assigned to specific roles to view and export content they would normally be unable to see, typically in the course of an investigation or litigation request. In the event that content must be provided to a third party, whether outside investigators or legal counsel, an export function allows content to be exported in an immutable format.
Office 365’s eDiscovery functionality is built around cases. When a case is created, you can put users or content on Legal Hold, create predefined Searches, and make multiple Exports in a variety of formats.
More fundamentally, eDiscovery is managed by assigning privileges via multiple roles, as well as by assigning individuals to a case. This allows for tight control on who can see what.
Permissions & Roles
One area that stymied me for a bit was ensuring that I, as a user, had the right privileges to make use of my eDiscovery case. Even as a Global Admin, at first I was not able to initially see the results of any queries in the case that I created. Essentially I had created a case as a Global Admin, but not assigned myself the proper role to preview results, and I had not assigned myself to a case.
In order to work with an eDiscovery case, a user will need access to the Security & Compliance Admin Center. Anyone with Global Administrator or Compliance Administrator roles should have this; individual users can also be granted access by using the Permissions panel under the Security & Compliance Admin Center, usually by assigning them to a specific eDiscovery role.
Within Security & Compliance Permissions are several pre-defined roles that bundle various permissions together; you can also create roles for customized sets of permissions. The entire list is worth a read, but two important ones are eDiscovery Manager and Data Investigator. In order for a user to make use of the cases created in Legal Hold, they should have one of these roles assigned.
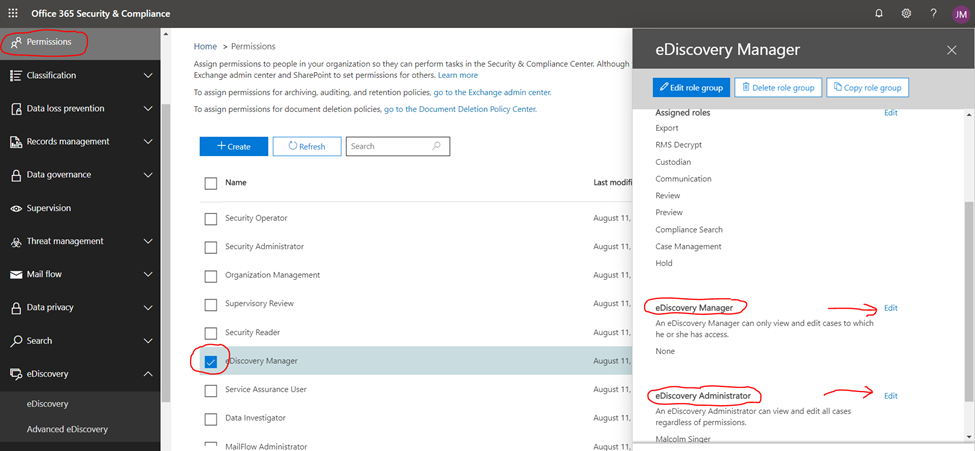
However, it is not enough to have these roles and permissions granted: a user must also be assigned to a case. All eDiscovery Managers are assigned to cases that they create, but not to other cases. Lower-level roles must be assigned to a case in order to access it. Imagine a large organization with dozens of cases active at any given time; the principle of least privilege requires that anyone involved in eDiscovery only be allowed access to the potentially sensitive content that is applicable to the cases that they are working on.
BONUS KNOWLEDGE: As if this weren’t confusing enough under the “eDiscovery Manager” role, there are actually two separate membership buckets: eDiscovery Manager and eDiscovery Administrator. Basically, these are two roles so similar that Microsoft concatenated them into a single role with bifurcated membership. They have the same privileges, except that an eDiscovery Manager can only access cases that they have created, while an eDiscovery Administrator can access all cases. Also, but “access”, in order to perform any work in the cases, an eDiscovery manager has to add themselves to the case.
So, to recap on required Permissions: access to Security & Compliance, assigned a specific role, and assigned to a case. Like most permissions models in Office 365, it’s worth having a think on what the business processes for eDiscovery are like in your organization before setting out how to administer them in Office 365. Have the vision before you build it.
Read more about permissions here.
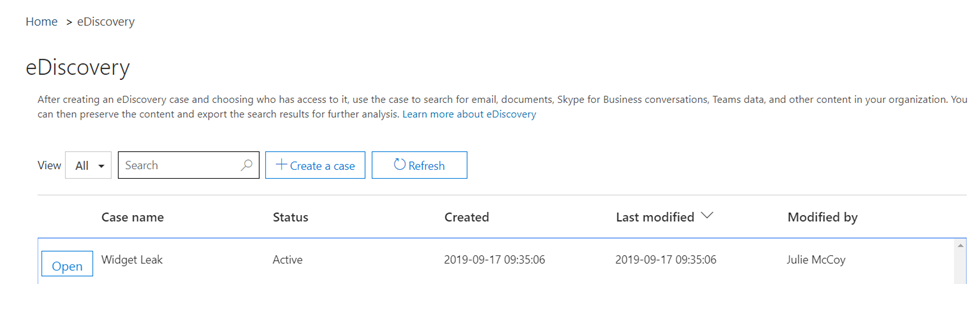
Case Management
To create a case, click on “Create a case”, and you’ll step through building out what I’m about to describe. In this example, I’ve already created a case, to investigate a leak of proprietary knowledge about a new widget being developed by the company.
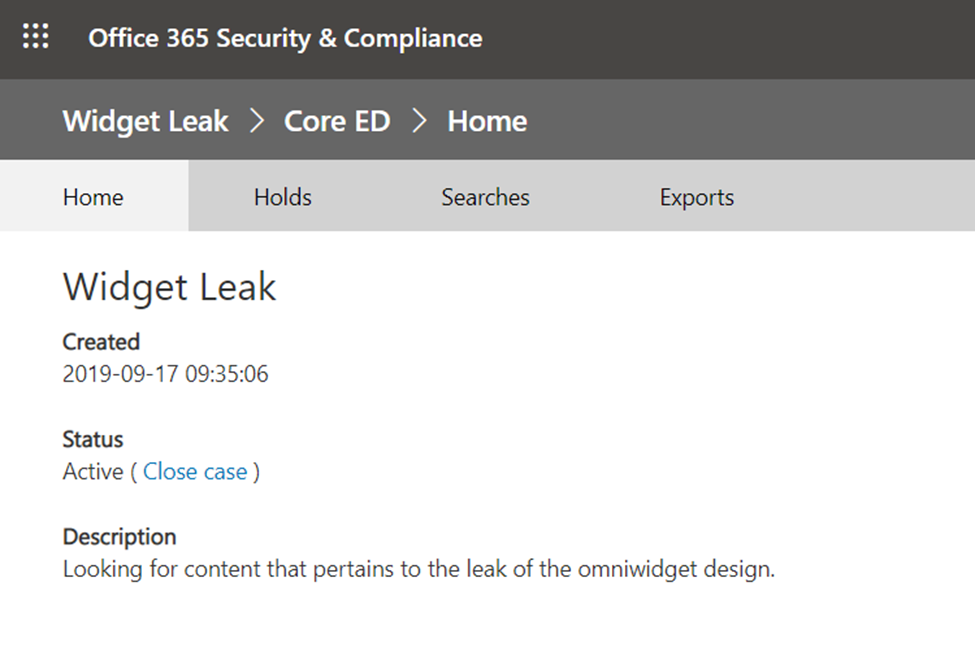
When you open a case, you can see some basic information about it, as well as navigate to tabs for the three basic activities in a case. When the case is complete and no longer needed, you can “close case”.
Legal Hold
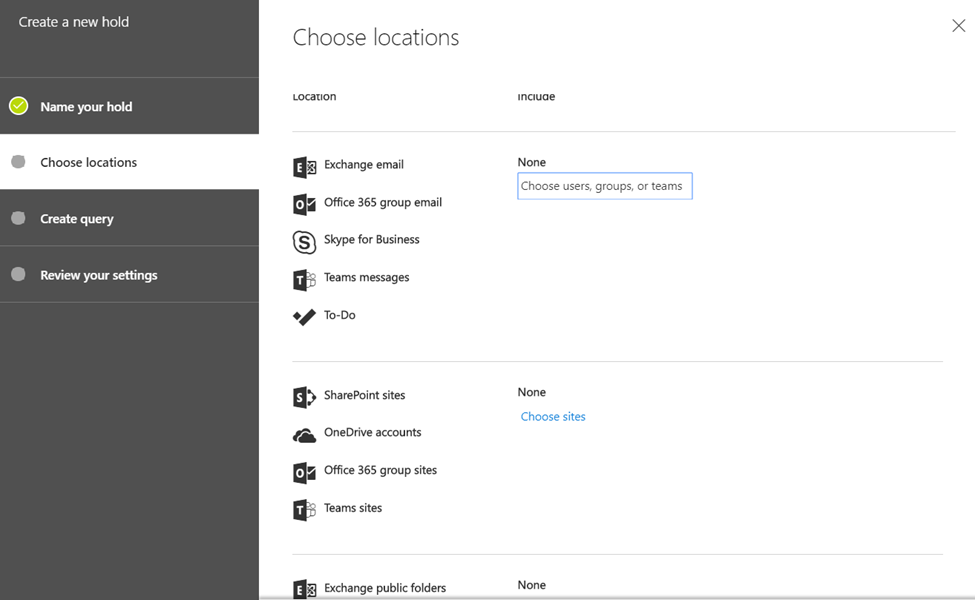
Legal Hold is a way to define content that should not be permanently deleted. This can be applied to users’ mailboxes, chats, and OneDrives, as well as to mailboxes, chats, and sites associated with an Office 365 Group or Team.
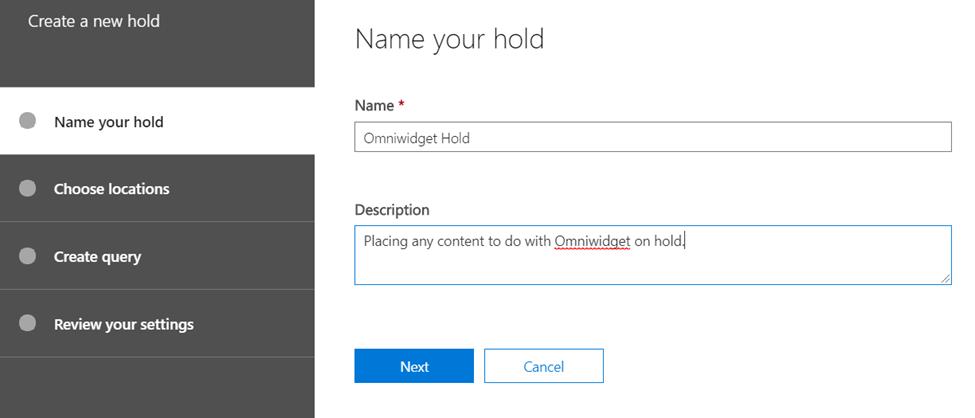
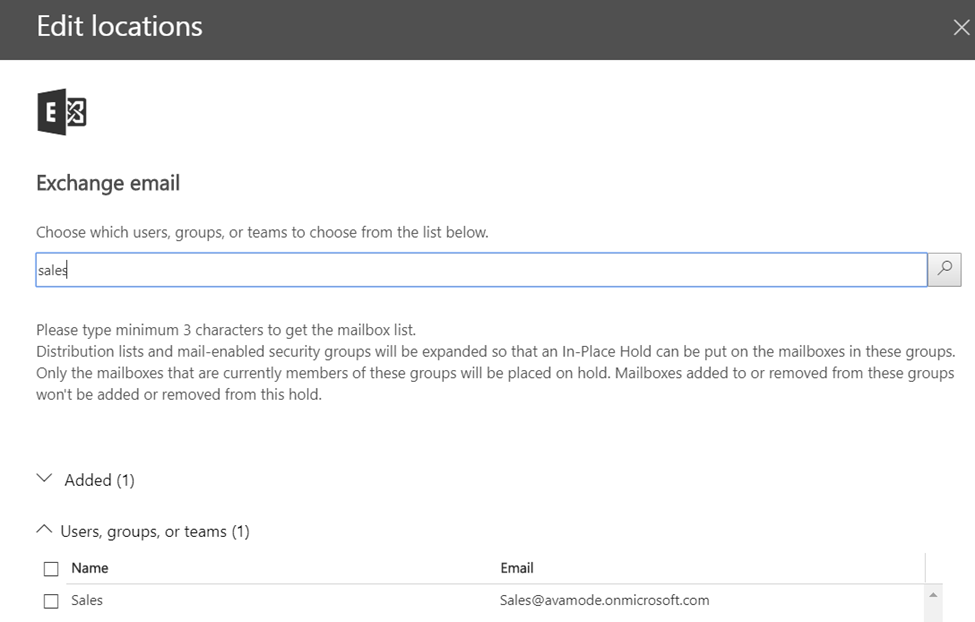
When creating a Legal Hold, the same Legal Hold can include entire content spaces (one or more mailboxes, one or more sites),or can place contents based on a query (everything sent by this person to these people with that word in the subject line). You can read more about Legal Hold here. For my purposes,since I have only a vague idea of what to look for, I’m going to place specific people and their Teams on Legal Hold
NOTE: for sites, you’ll need the full URL path to the site. Unlike user mailboxes, there’s no “picker” functionality.
Searches
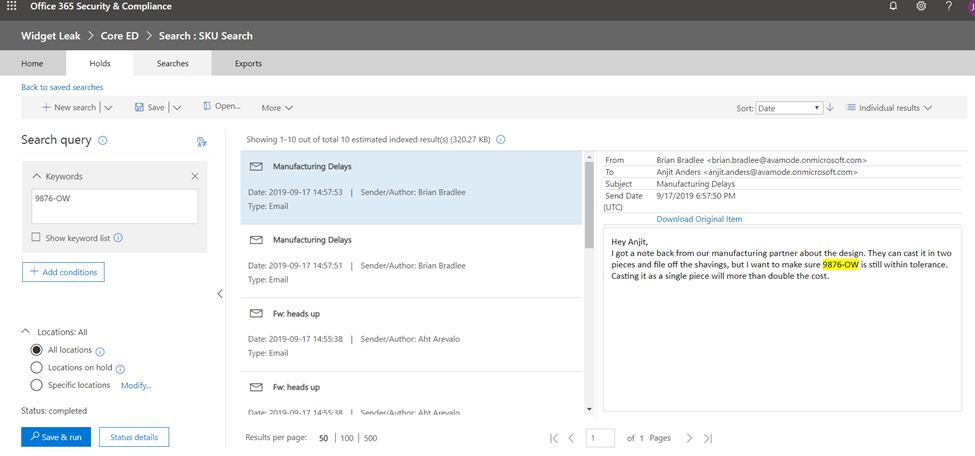
Once a user has an assigned role and can access a case, they can view details about Legal Holds related to the case, and create new ones if they have the right permissions. However, the bulk of their work is more likely to be in creating and executing search queries.
In the example below, I created a search for a specific part number, which in this example is the part number for the new widget being released. Right off the bat I see several emails between Aht, the head of sales, and Brian, the head of product.
Export
An eDiscovery user may need to export what they find, typically to put into a format that others can use, internally or externally. From export, a user can either export the actual results, or a report of them.
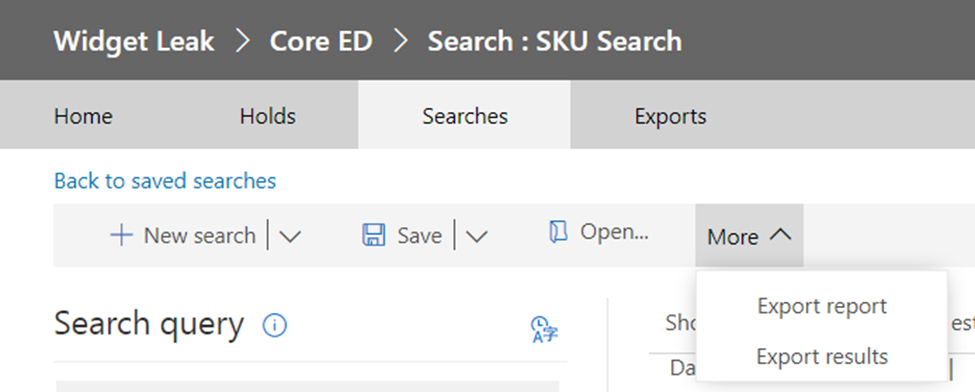
A Report is just a list of what was found; Results are the actual items. When Exporting Results, there are a few switches to throw. Basically:
Export everything, but not encrypted or unrecognizable formats.
Export everything from the search, including encrypted or unrecognizable formats.
Export only the encrypted or unrecognizable formats.
Exchange formatted items can be exported in ways that bundle content in various combinations of .pst files.
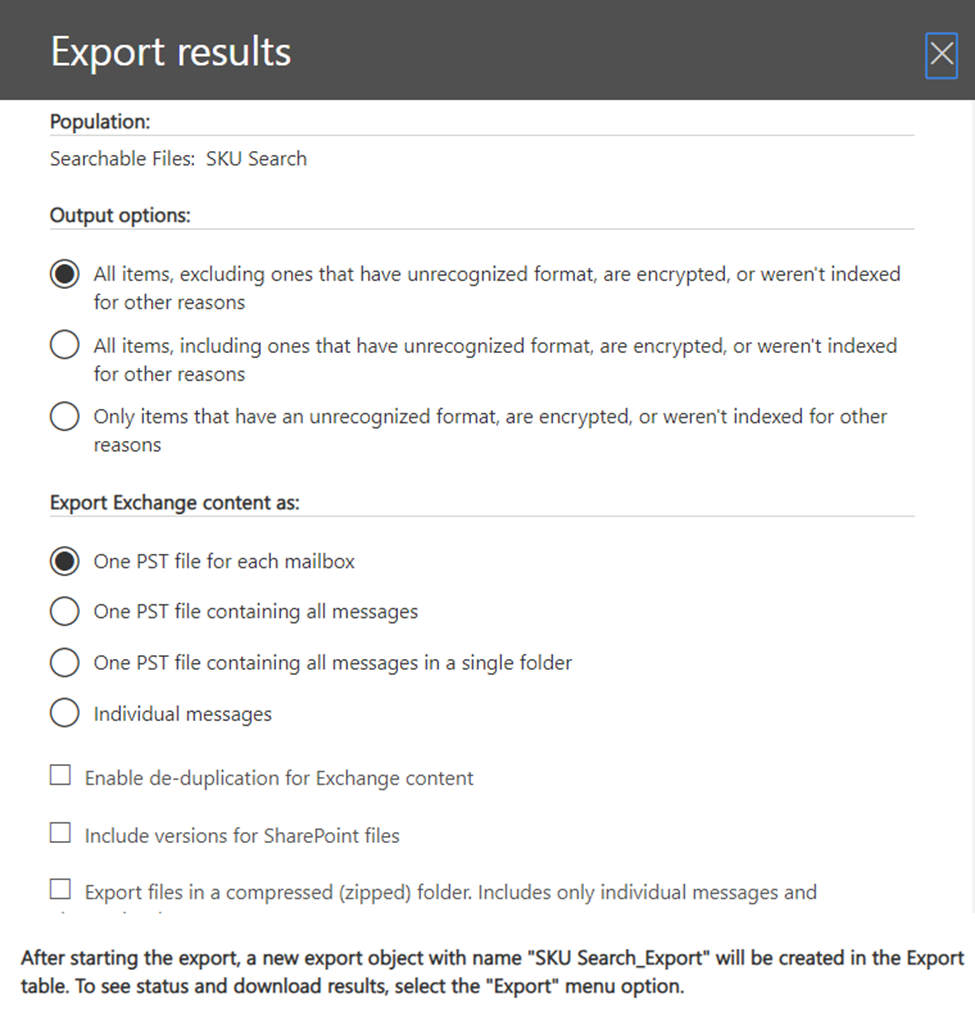
Note the flag for “including versions for SharePoint files”. Some investigations may ask for all versions of a file.
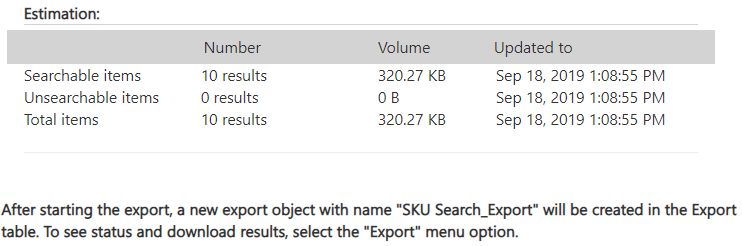
Further down in the Export Results flyout is a short bit giving you a preview of how much content will be exported.
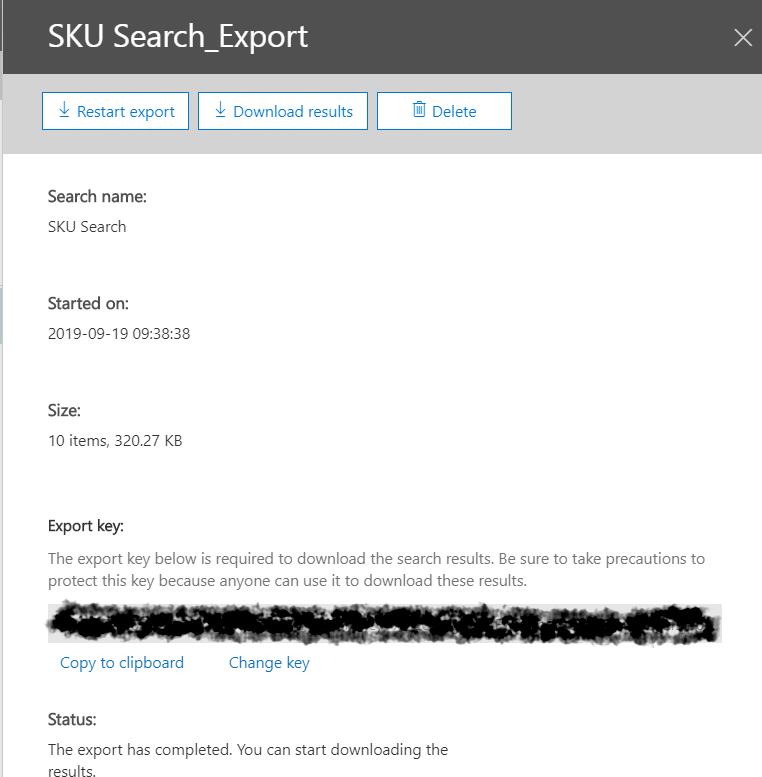
Once content has been exported, the export will show up under the Exports tab. That’ll be our final stop on our journey of eDiscovery.
In order to download results, the person downloading the content will need the key listed under the export. The key can be changed in the event that, for example, there is staff change in the recipient’s organization. Additionally, Office 365 will warn that only Edge and Internet Explorer web browsers are supported.
Summary
Office 365’s eDiscovery options may appear simplistic at first, but they are in fact quite powerful. Users may be assigned very specific privileges with very limited scope, or be given wide range to search all workloads in 365 for relevant content. It’s a highly-configurable solution that allows organizations to tailor their usage to their business processes for finding content relevant to investigations and litigation.
Content can be searched for on a variety of criteria, including retention and sensitivity labels. Legal Hold prevents the permanent deletion of content, and content can be exported in an immutable form. Some organizations may rely on eDiscovery as a singular solution, as one of several solutions, or simply as a means to export content from Office 365 into a third-party solution that can manage multiple content sources.